Generate 448 Bit Encryption Key
- Generate 448 Bit Encryption Key File
- 256 Bit Encryption
- 2048 Bit Encryption
- Generate 448 Bit Encryption Key Software
Creating and managing keys is an important part of the cryptographic process. Symmetric algorithms require the creation of a key and an initialization vector (IV). The key must be kept secret from anyone who should not decrypt your data. The IV does not have to be secret, but should be changed for each session. Asymmetric algorithms require the creation of a public key and a private key. The public key can be made public to anyone, while the private key must known only by the party who will decrypt the data encrypted with the public key. This section describes how to generate and manage keys for both symmetric and asymmetric algorithms.
Symmetric Keys
The symmetric encryption classes supplied by the .NET Framework require a key and a new initialization vector (IV) to encrypt and decrypt data. Whenever you create a new instance of one of the managed symmetric cryptographic classes using the parameterless constructor, a new key and IV are automatically created. Anyone that you allow to decrypt your data must possess the same key and IV and use the same algorithm. Generally, a new key and IV should be created for every session, and neither the key nor IV should be stored for use in a later session.
If you enter a VLK key for Windows 10 Pro on Windows 10 Home, it will not be accepted. What you can do is enter the Windows 10 Pro upgrade key, VK7JG-NPHTM-C97JM-9MPGT-3V66T, let it. Windows xp vlk key generator.
To communicate a symmetric key and IV to a remote party, you would usually encrypt the symmetric key by using asymmetric encryption. Sending the key across an insecure network without encrypting it is unsafe, because anyone who intercepts the key and IV can then decrypt your data. For more information about exchanging data by using encryption, see Creating a Cryptographic Scheme.
- There are multiple ways of generating an encryption key. Most implementations rely on a random object. All examples mentioned here use a secure cryptographic randomizer.
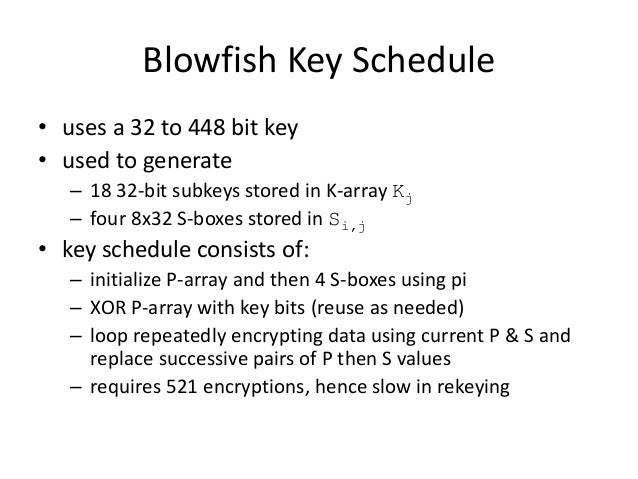
- It is free algorithm available to everyone. Blowfish algorithm has gained lots of popularity especially due to its free license. It uses a variable lenght key, from 32 to 448-bit, although most of commercial and non comercial products uses for the strongest 448 bit encryption with blowfish.
The following example shows the creation of a new instance of the TripleDESCryptoServiceProvider class that implements the TripleDES algorithm.
When the previous code is executed, a new key and IV are generated and placed in the Key and IV properties, respectively.
Sometimes you might need to generate multiple keys. In this situation, you can create a new instance of a class that implements a symmetric algorithm and then create a new key and IV by calling the GenerateKey and GenerateIV methods. The following code example illustrates how to create new keys and IVs after a new instance of the symmetric cryptographic class has been made.
When the previous code is executed, a key and IV are generated when the new instance of TripleDESCryptoServiceProvider is made. Another key and IV are created when the GenerateKey and GenerateIV methods are called.
How To Generate 4096 bit Secure Ssh Key with Ssh Keygen. The encryption power comes from key bit size or length. In this tutorial we will look how to create 4096 bit keys. Generate 4098 Bit Key. In this example we will generate very secure key. This key size will be 4096 bit. 4096 bit keys are a lot more secure than 2048 or 1024 bit keys. CREATE DATABASE ENCRYPTION KEY (Transact-SQL); 2 minutes to read +2; In this article. APPLIES TO: SQL Server Azure SQL Database Azure Synapse Analytics (SQL DW) Parallel Data Warehouse. Creates an encryption key that is used for transparently encrypting a database. A computer encryption key is nothing more than a string of bits where each bit can have a value of either 0 or 1. The number of possible values for a key is simply the total number of values that the key can have. So our one-bit long key can only have two possible values – 0 and 1.
Asymmetric Keys
The .NET Framework provides the RSACryptoServiceProvider and DSACryptoServiceProvider classes for asymmetric encryption. These classes create a public/private key pair when you use the parameterless constructor to create a new instance. Asymmetric keys can be either stored for use in multiple sessions or generated for one session only. While the public key can be made generally available, the private key should be closely guarded.
A public/private key pair is generated whenever a new instance of an asymmetric algorithm class is created. After a new instance of the class is created, the key information can be extracted using one of two methods:
Generate 448 Bit Encryption Key File
The ToXmlString method, which returns an XML representation of the key information.
Company of heroes opposing fronts key generator reviews. Cd-key company of heroes opposing fronts Hello,i have buy company of heroes NO steam. They released the steam version, then I insert the code of company of heroes to activate the new version, but it tells me the wrong code. Download now the serial number for Company of Heroes:Opposing Fronts. All serial numbers are genuine and you can find more results in our database for Company software. Updates are issued periodically and new results might be added for this applications from our community.
The ExportParameters method, which returns an RSAParameters structure that holds the key information.
Both methods accept a Boolean value that indicates whether to return only the public key information or to return both the public-key and the private-key information. An RSACryptoServiceProvider class can be initialized to the value of an RSAParameters structure by using the ImportParameters method.
256 Bit Encryption
Asymmetric private keys should never be stored verbatim or in plain text on the local computer. If you need to store a private key, you should use a key container. For more on how to store a private key in a key container, see How to: Store Asymmetric Keys in a Key Container.
The following code example creates a new instance of the RSACryptoServiceProvider class, creating a public/private key pair, and saves the public key information to an RSAParameters structure.
2048 Bit Encryption