What Generates The Key Pair Used In Asymmetric Cryptography
- What Generates The Key Pair Used In Asymmetric Cryptography Meaning
- What Generates The Key Pair Used In Asymmetric Cryptography Center
- What Generates The Key Pair Used In Asymmetric Cryptography In Computer
2.1.4 Hybrid Encryption. To get the speed of symmetric key operations in open systems, key exchange protocols have been developed that initially use public-key operations to establish a shared key for a given communication session and then use that shared key (under, e.g., AES) for the remainder of the session. RSA key pair generation is generally only performed once. A new RSA key pair only need to be generated when the old pair is revoked. Such a key pair can be used to encrypt/decrypt a lot of messages. The RSA public and private key are linked; it is not possible to generate new private keys that use the same public key. Which of the following generates the key pair used in asymmetric cryptography? CA CRL OCSP CPS CSP. Which cryptography system generates encryption keys that could be used with DES, AES, IDEA, RC5 or any other symmetric cryptography solution? MerkleHellman Knapsack RSA Elliptical Curve. GenerateDataKeyPair Generates a unique asymmetric data key pair. The GenerateDataKeyPair operation returns a plaintext public key, a plaintext private key, and a copy of the private key that is encrypted under the symmetric CMK you specify.
Yes, you can use PBKDF to derive keys for asymmetric encryption too. This is most convenient with encryption schemes such as ElGamal, IES or their elliptic curve variants, where a private key is simply a random number chosen from a given interval. In principle, you could do the same with RSA too, but the key generation process is more cumbersome. Mar 11, 2020 Public-key cryptography, or asymmetric encryption, is a cryptographic system based on pairs of keys, a public and a private key. The main use cases of asymmetric encryption are encrypting.
Key generation is the process of generating keys in cryptography. A key is used to encrypt and decrypt whatever data is being encrypted/decrypted.
A device or program used to generate keys is called a key generator or keygen.
Generation in cryptography[edit]
Modern cryptographic systems include symmetric-key algorithms (such as DES and AES) and public-key algorithms (such as RSA). Symmetric-key algorithms use a single shared key; keeping data secret requires keeping this key secret. Public-key algorithms use a public key and a private key. The public key is made available to anyone (often by means of a digital certificate). A sender encrypts data with the receiver's public key; only the holder of the private key can decrypt this data.
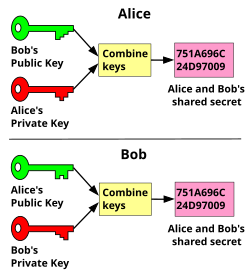
Since public-key algorithms tend to be much slower than symmetric-key algorithms, modern systems such as TLS and SSH use a combination of the two: one party receives the other's public key, and encrypts a small piece of data (either a symmetric key or some data used to generate it). The remainder of the conversation uses a (typically faster) symmetric-key algorithm for encryption.
Computer cryptography uses integers for keys. In some cases keys are randomly generated using a random number generator (RNG) or pseudorandom number generator (PRNG). A PRNG is a computeralgorithm that produces data that appears random under analysis. PRNGs that use system entropy to seed data generally produce better results, since this makes the initial conditions of the PRNG much more difficult for an attacker to guess. Another way to generate randomness is to utilize information outside the system. veracrypt (a disk encryption software) utilizes user mouse movements to generate unique seeds, in which users are encouraged to move their mouse sporadically. In other situations, the key is derived deterministically using a passphrase and a key derivation function.
Windows 10 product ultimate key generator. Many modern protocols are designed to have forward secrecy, which requires generating a fresh new shared key for each session.
Classic cryptosystems invariably generate two identical keys at one end of the communication link and somehow transport one of the keys to the other end of the link.However, it simplifies key management to use Diffie–Hellman key exchange instead.
The simplest method to read encrypted data without actually decrypting it is a brute-force attack—simply attempting every number, up to the maximum length of the key. Therefore, it is important to use a sufficiently long key length; longer keys take exponentially longer to attack, rendering a brute-force attack impractical. Currently, key lengths of 128 bits (for symmetric key algorithms) and 2048 bits (for public-key algorithms) are common.
Generation in physical layer[edit]
Wireless channels[edit]
A wireless channel is characterized by its two end users. By transmitting pilot signals, these two users can estimate the channel between them and use the channel information to generate a key which is secret only to them.[1] The common secret key for a group of users can be generated based on the channel of each pair of users.[2]
Optical fiber[edit]
A key can also be generated by exploiting the phase fluctuation in a fiber link.[clarification needed]
See also[edit]
- Distributed key generation: For some protocols, no party should be in the sole possession of the secret key. Rather, during distributed key generation, every party obtains a share of the key. A threshold of the participating parties need to cooperate to achieve a cryptographic task, such as decrypting a message.
References[edit]
- ^Chan Dai Truyen Thai; Jemin Lee; Tony Q. S. Quek (Feb 2016). 'Physical-Layer Secret Key Generation with Colluding Untrusted Relays'. IEEE Transactions on Wireless Communications. 15 (2): 1517–1530. doi:10.1109/TWC.2015.2491935.
- ^Chan Dai Truyen Thai; Jemin Lee; Tony Q. S. Quek (Dec 2015). 'Secret Group Key Generation in Physical Layer for Mesh Topology'. 2015 IEEE Global Communications Conference (GLOBECOM). San Diego. pp. 1–6. doi:10.1109/GLOCOM.2015.7417477.
What Generates The Key Pair Used In Asymmetric Cryptography Meaning
RSA(Rivest-Shamir-Adleman) is an Asymmetric encryption technique that uses two different keys as public and private keys to perform the encryption and decryption. With RSA, you can encrypt sensitive information with a public key and a matching private key is used to decrypt the encrypted message. Asymmetric encryption is mostly used when there are 2 different endpoints are involved such as VPN client and server, SSH, etc.
Below is an online tool to perform RSA encryption and decryption as a RSA calculator.
For Java implementation of RSA, you can follow this article.
The main problem with other product key hacking software is that it is small in size. Windows 8.1 professional key generator reviews. And it does not have too much space on the hard disk after installation. The Windows 10 product key activator is amazing and valuable for all computers, such as home, office, educational institutions, organizations and more.You may also like:The Windows 10 product key generator can generate functional product keys that are more powerful and excellent instead of other Windows 10 loader generators. It saves a lot of time discovering a useful and functional product for both operating systems.
First, we require public and private keys for RSA encryption and decryption. Hence, below is the tool to generate RSA key online. It generates RSA public key as well as the private key of size 512 bit, 1024 bit, 2048 bit, 3072 bit and 4096 bit with Base64 encoded.
By default, the private key is generated in PKCS#8 format and the public key is generated in X.509 format.
Generate RSA Key Online
Public Key
RSA Encryption and Decryption Online
Below is the tool for encryption and decryption. Either you can use the public/private keys generated above or supply your own public/private keys.
Any private or public key value that you enter or we generate is not stored on this site, this tool is provided via an HTTPS URL to ensure that private keys cannot be stolen.
This tool provides flexibility for RSA encrypt with public key as well as private key along with RSA decrypt with public or private key.
If You Appreciate What We Do Here On Devglan, You Can Consider:
What Generates The Key Pair Used In Asymmetric Cryptography Center
- Like us at: or follow us at
- Share this article on social media or with your teammates.
- We are thankful for your never ending support.
Usage Guide - RSA Encryption and Decryption Online
In the first section of this tool, you can generate public or private keys. To do so, select the RSA key size among 515, 1024, 2048 and 4096 bit click on the button. This will generate the keys for you.
For encryption and decryption, enter the plain text and supply the key. As the encryption can be done using both the keys, you need to tell the tool about the key type that you have supplied with the help of radio button. By default, public key is selected. Then, you can use the cipher type to be used for the encryption. The different cipger options are RSA, RSA/ECB/PKCS1Padding and RSA/ECB/OAEPWithSHA-1AndMGF1Padding. Now, once you click the encrypt button the encrypted result will be shown in the textarea just below the button.
Remember, the encrypted result is by default base64 encoded.
Similarly, for decryption the process is same. Here, you need to enter the RSA encrypted text and the result will be a plain-text. You have both options to decrypt the encryption with public and private keys.
References