Windows Iis Generate Private Key
Sep 11, 2018 To generate a public and private key with a certificate signing request (CSR), run the following OpenSSL command: openssl req –out certificatesigningrequest.csr -new -newkey rsa:2048 -nodes -keyout privatekey.key. FKCS12 files are used to export/import certificates in Windows IIS. Otherwise Follow the instructions H ow To Export an SSL Certificate With Private Key (pfx) Using MMC On Windows to get that intermediate into the pfx file. To Export the SSL Certificate as a pfx file from the IIS manager perform the following. Go to Start Administrative Tools.
Purpose: Recovering a missing private key in IIS environment.
For Microsoft II8
(Jump to the solution)
Cause:
Entrust SSL certificates do not include a private key. The private key resides on the server that generated the Certificate Signing Request (CSR). When installed correctly, the Server Certificate will match up with the private key as displayed below:
If the private key is missing, the circled message indicating a good correspondence with private key will be missing as shown here:
- How to: Create a public-private key pair.; 2 minutes to read; In this article. To sign an assembly with a strong name, you must have a public/private key pair. This public and private cryptographic key pair is used during compilation to create a strong-named assembly. You can create a key pair using the Strong Name tool (Sn.exe).
- Final step is binding the SSL cert to the site's port 443 connection in the IIS console. If you happen to need the private key, you can use the 'Export' function to create a.key file or a PFX file which includes both your domain certificate and the private key. Some firewall devices require a PKCS#12 file over the PFX.
- Note: if the CSR was generated this way but the certificate needs to be installed on a Windows server (i.e. IIS), you’ll need to generate the PFX file from the certificate and Private key. To do that, use this command: openssl pkcs12 -export -out.your certificate.pfx -inkey server.key -in.your certificate.p7b.
- Windows/IIS On Windows servers, the OS manages the certificate for you in a hidden file, but you can export a.PFX file that contains both the certificate and the private key. Open the Microsoft Management Console (MMC).
A missing private key could mean:
- The certificate is not being installed on the same server that generated the CSR.
- The pending request was deleted from IIS.
- The certificate was installed through the Certificate Import Wizard rather than through IIS.
In this technote we do not discuss how to determine the reason the private key is missing. Select the link corresponding to each reason listed above for more information.
There's a video for this guide. Watch the video here.
1) Snap-In Configuration
2) Import the Server Certificate
3) Recover the private key
Use the following steps to add the Certificates snap-in:
1. Click Start, and then search for Run.2. Type in mmc and click OK.
3. From the File menu, choose Add/Remove Snap-in.
4. Select Certificates and then Add.
5. Choose the Computer account option and click Next.
6. Select Local Computer and then click Finish.
7. Click Close, and then click OK. The snap-in for Certificates (Local Computer) appears in the console.
Use the following steps to import your Server Certificate into the Personal certificate store. If the Server Certificate has already been imported into the Personal store, you may skip this step.
From the MMC console opened in the above steps:
1. Expand the Certificates (Local Computer) tree in the left preview panel.
2. Right-click Personal and select All Tasks > Import.
3. The Certificate Import Wizard appears. Click Next.
4. Browse to the location of your Server Certificate file and click Next.
5. Select Place all certificates in the following store and click Next.
6. Click Finish to complete the Certificate Import Wizard.
7. A dialog box appears indicating the import was successful. Click OK.Use the following steps to recover your private key using the certutil command.
1. Locate your Server Certificate file by opening Microsoft Internet Information Services Manager, then on the right side select Tools > Internet Information Services (IIS) Manager.
2. Once in IIS Manager, select your server, then on the right side, Server Certificates. You will see all certificates currently on that server. Scroll over the certificate you are trying to install, right click, then select View.
3. There, you can view the certificate information. As you can see, there is no indication of a good correspondence with the private key.
4. Click the Details tab. Write down the serial number of the certificate.
5. We will need to recover the private key using a command prompt. In order to recover the key, we must do so using command prompt as an administrator. To do so, slick Start, then on then open all App. Under Windows System, find Command Prompt. Right click Command prompt and then Run as administrator. Confirm the action and continue.
6. Make sure you are on the right directory in command prompt.
e.g., if your server directory is “c:/users/srv2012_r2_std_x64”, on the command line type “cd c:/users/srv2012_r2_std_x64”. Note that “cd” is the command used to change directories in command prompt.
7. Now that we are in the right place, enter the following command at the prompt: certutil –repairstore my <serial number> where <serial number> is the serial number obtained in Step 2 with spaces removed.
8. If Windows is able to recover the private key, you see the message:
CertUtil: -repairstore command completed successfully.
If your private key was recovered successfully, your Server Certificate installation is complete.
If the private key was not recovered successfully, you will need to generate a new Certificate Signing Request and submit it to Entrust Datacard to have your certificate re-issued, or re-issue the certificate using your ECS Enterprise account.
Check that your Certificate has been successfully installed by testing it on the Entrust SSL Install Checker.
If you have any questions or concerns please contact the Entrust Certificate Services Supportdepartment for further assistance:
Hours of Operation:
Sunday 8:00 PM ET to Friday 8:00 PM ET
North America (toll free): 1-866-267-9297
Outside North America: 1-613-270-2680 (or see the list below)
Mann co supply crate key generator download free. NOTE: It is very important that international callers dial the UITF format exactly as indicated. Do not dial an extra '1' before the '800' or your call will not be accepted as an UITF toll free call.
Country | Number |
Australia | 0011 - 800-3687-7863 1-800-767-513 |
Austria | 00 - 800-3687-7863 |
Belgium | 00 - 800-3687-7863 |
Denmark | 00 - 800-3687-7863 |
Finland | 990 - 800-3687-7863 (Telecom Finland) |
France | 00 - 800-3687-7863 |
Germany | 00 - 800-3687-7863 |
Hong Kong | 001 - 800-3687-7863 (Voice) |
Ireland | 00 - 800-3687-7863 |
Israel | 014 - 800-3687-7863 |
Italy | 00 - 800-3687-7863 |
Japan | 001 - 800-3687-7863 (KDD) |
Korea | 001 - 800-3687-7863 (Korea Telecom) |
Malaysia | 00 - 800-3687-7863 |
Netherlands | 00 - 800-3687-7863 |
New Zealand | 00 - 800-3687-7863 0800-4413101 |
Norway | Generate an api key for each registered user guide. 00 - 800-3687-7863 |
Singapore | 001 - 800-3687-7863 |
Spain | 00 - 800-3687-7863 |
Sweden | 00 - 800-3687-7863 (Telia) |
Switzerland | 00 - 800-3687-7863 |
Taiwan | 00 - 800-3687-7863 |
United Kingdom | 00 - 800-3687-7863 |
The following instructions will guide you through the CSR generation process on Microsoft IIS 7. To learn more about CSRs and the importance of your private key, reference our Overview of Certificate Signing Request article. If you already generated the CSR and received your trusted SSL certificate, reference our SSL Installation Instructions and disregard the steps below.
1. Open Internet Information Services (IIS) Manager
Click Start, Control Panel, Administrative Tools, and then select Internet Information Services (IIS) Manager.
2. Select the server where you want to generate the certificate
In the left Connections menu, select the server name (host) where you want to generate the request.
3. Navigate to Server Certificates
In the center menu, click the Server Certificates icon under the Security section near the bottom.
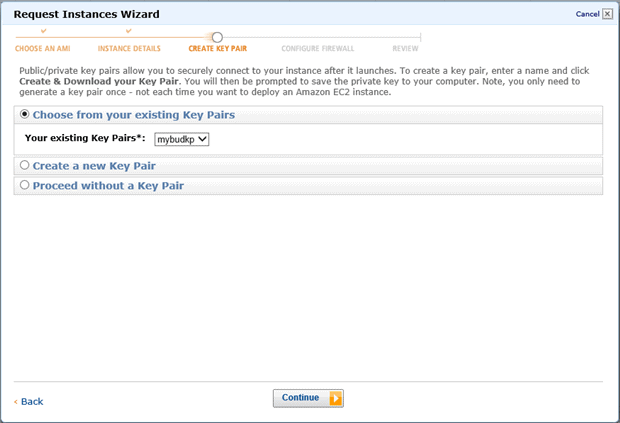
4. Select Create a New Certificate
In the right Actions menu, click Create Certificate Request.
5. Enter your CSR details
In the Distinguished Name Properties window, enter in the required CSR details and then click Next.
Note: To avoid common mistakes when filling out your CSR details, reference our Overview of Certificate Signing Request article.
6. Select a cryptographic service provider and bit length
In the Cryptographic Service Provider Properties window, select Microsoft RSA SChannel Cryptographic Provider and Bit Length of 2048, then click Next.
Note: Bit Length: 2048 is the current industry standard. You may choose a larger key size, but only if you have a requirement to do so, as longer key lengths increase latency and may reduce compatibility.
7. Save the CSR
Click Browse to specify the location where you want to save the CSR as a “.txt” file and click Finish.
8. Generate the order
Locate and open the newly created CSR from the specified location you choose in a text editor such as Notepad and copy all the text including:
Return to the Generation Form on our website and paste the entire CSR into the blank text box and continue with completing the generation process.
Upon generating your CSR, your order will enter the validation process with the issuing Certificate Authority (CA) and require the certificate requester to complete some form of validation depending on the certificate purchased. For information regarding the different levels of the validation process and how to satisfy the industry requirements, reference our validation articles.
Windows Iis Generate Private Key For Putty
After you complete the validation process and receive the trusted SSL Certificate from the issuing Certificate Authority (CA), proceed with the next step using our SSL Installation Instructions for Microsoft IIS 7.